How to use GPO to enable Windows Lock Screen after inactivity? Core
In this post, we’ll show you how to use Group Policy to setup automatic screen (session) lock on domain workstations and servers. An important aspect of information security is locking the computer screen when the user is inactive (idle). When the user needs to leave the office for a short time, he may forget to lock his desktop (using the keyboard shortcut Win + L).
In this circumstance, every adjacent employee or client has access to his information. This problem will be fixed by enforcing the auto-lock screen policy. The user’s desktop will be automatically locked after a period of inactivity (idle), and the user will need to re-enter their domain password to return to the session.
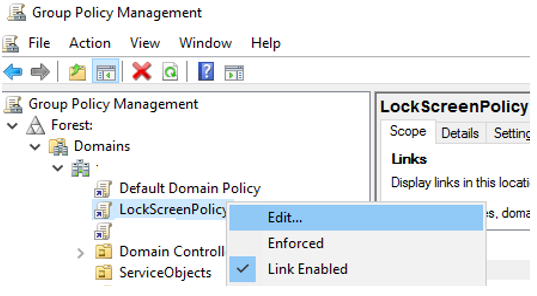
To handle screen lock settings, let’s build and set a domain Group Policy:
Create a new GPO object (LockScreenPolicy) and link it to the domain root (or the Users OU) in the Group Policy Management console (gpmc.msc).
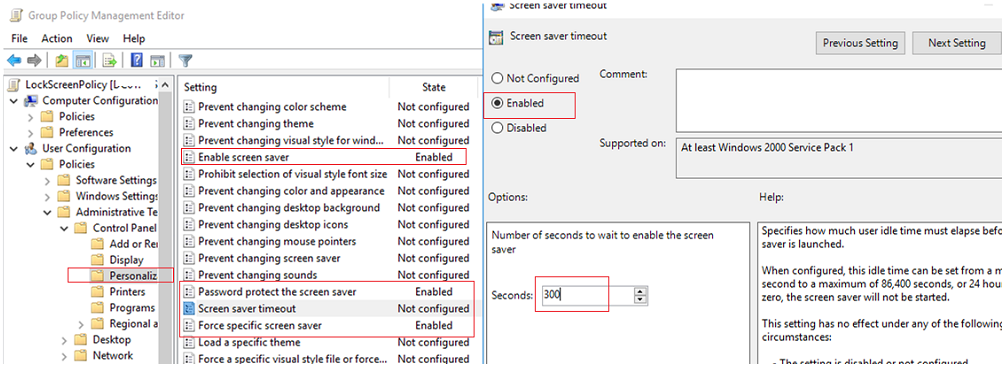
- Make changes to the policy Go to User Configuration -> Policies -> Administrative Templates -> Control Panel -> Personalization and make changes.
- In the GPO area, there are some options for managing screen saver and screen lock settings:Enable screen saver
- Password protect the screen saver — requires a password to unlock a computer;
- Screen saver timeout – specifies the amount of time in seconds after which a screen saver will be enabled and a computer will be locked if a user is inactive;
- Force specific screen saver – specifies the screen saver file to be used. Scrnsave.scr is the most common (you can make a slideshow screen saver using GPO)
- Prohibits users from altering the screen saver settings — prevents users from altering the screen saver settings.
In the Screen saver timeout policy, enable all rules and set a computer idle time. I’ve input the number 300. It means that after 5 minutes, user sessions will be automatically locked.
- Wait for the Group Policy settings on the clients to be updated, or manually refresh them with the command gpupdate /force. Screen saver and screen lock settings will be blocked from editing in the Windows interface after the GPO is activated, and user sessions will be locked after 5 minutes of inactivity.
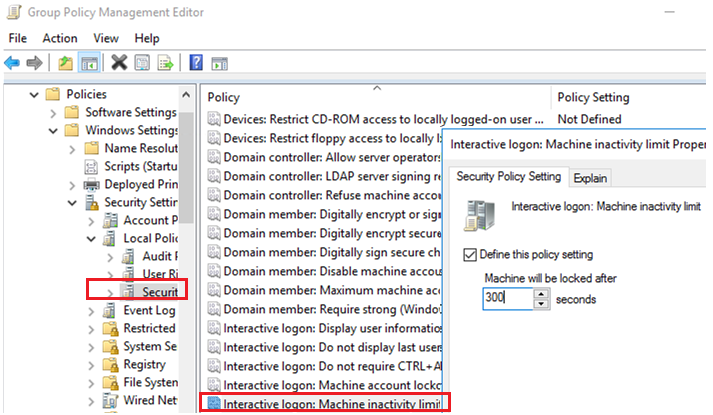
- There is a distinct computer security policy in Windows Server 2012/Windows 8 or newer that sets a computer inactivity time after which it is locked. This policy is called Interactive logon: This policy is You may locate it in Computer Configuration -> Windows Settings -> Security Settings -> Local Policies -> Security Options
You may need to set up various lock policies for various user groups in some circumstances. For example, office workers’ screens should be locked after 10 minutes, but production or operators’ screens should never be locked. You can use GPO Security Filtering or Item Level Targeting in GPP to implement such a strategy. Let’s take a closer look at the latter.
Instead of utilising GPO, you can utilise the registry to configure computer lock settings and then GPO to deploy the registry settings to users’ computers. The registry settings listed below correspond to the policies mentioned above. They can be found in the
HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\Control Panel\Desktop:
A REG SZ option named ScreenSaverIsSecure = is used to protect the screen saver with a password.
ScreenSaveTimeout = 300 is a REG SZ parameter for the screen saver timeout.
ScreenSaveActive = 1 and SCRNSAVE.EXE = scrnsave.scr are REG SZ parameters that force a certain screen saver.
To disable the screen lock policy, create a domain security group (grp not-lock-prod) and add users to it. In the applicable GPO area (User Configuration -> Preferences -> Windows Settings -> Registry), create the registry parameters specified above. Set the policy not to apply for the specific security group for each parameter using Item Level Targeting.
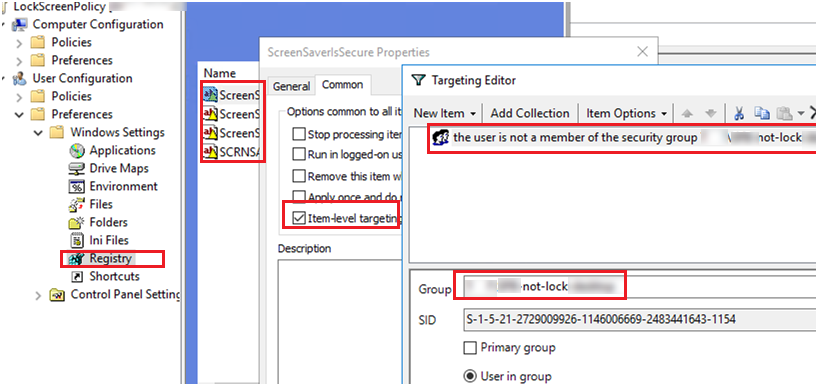
You’ll also need to add four more registry parameters with the value REG SZ 0 to force the group grp not-lock-prod to disable
At Velan, our server support engineers can manage group policy on your server. If you are interested in our service, please fill the Quick connect form to get in touch with us.
Categories
- Applications (5)
- Magento (1)
- Cloud (19)
- AWS (17)
- Google Drive (1)
- Office365 (1)
- Database (4)
- DNS (2)
- Cloudflare (2)
- Zone Lockdown (1)
- Cloudflare (2)
- Linux (42)
- DirectAdmin (1)
- Server (40)
- Core (10)
- cPanel / WHM (6)
- Dockers (3)
- Security (7)
- zimbra (1)
- SSL (1)
- PHP (1)
- Windows (14)
- Windows Server (1)
- IIS (1)
- Application Pool (1)
- IIS (1)




